M
There were reports in the news recently that a computer virus caused serious problems earlier this month for an electric utility in NSW and Queensland in Australia. The news reports that I have seen about it were vague and conflicting. I was wondering if anyone had any solid news on what went on (as opposed to the rumours that are floating around).
The story as I understand it is:
1) An electric utility in NSW and Queensland in Australia was severely affected by a computer virus at the beginning of October.
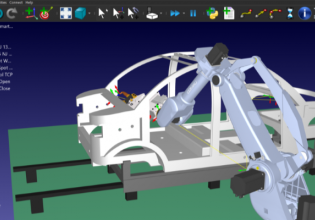
2) The problem apparently originated in their business systems.
3) There was no effective separation between the business systems and the control systems.
4) The operating system which the control system runs on used Solaris. However, the operator stations which were used to interact with the controls ran X terminal software on PCs using MS Windows. These MS Windows workstations were directly vulnerable to the virus.
5) As a result of the above, the virus affected the operator control stations and prevented the operators from monitoring or interacting with the control system (which itself was still functioning).
6) Outside help had to be brought in to deal with the problem, and dealing with it was a long and expensive process.
The news reports that I have seen so far on this have been vague and confused. I was hoping that something more solid would turn up later, but so far nothing has.
I was wondering if anyone had any substantial information on:
a) What took place, particularly with regards to how it started,
b) What was affected,
c) How long it took to get under control, and
d) what temporary and permanent measures were taken to deal with it.
It would also be interesting to hear what measures anyone else has taken to prevent a similar or more serious problem from occurring in their own SCADA, HMI, or other system. I suspect that the typical SCADA, HMI, or plant historian system would be much more vulnerable than was the case in this instance.
The story as I understand it is:
1) An electric utility in NSW and Queensland in Australia was severely affected by a computer virus at the beginning of October.
2) The problem apparently originated in their business systems.
3) There was no effective separation between the business systems and the control systems.
4) The operating system which the control system runs on used Solaris. However, the operator stations which were used to interact with the controls ran X terminal software on PCs using MS Windows. These MS Windows workstations were directly vulnerable to the virus.
5) As a result of the above, the virus affected the operator control stations and prevented the operators from monitoring or interacting with the control system (which itself was still functioning).
6) Outside help had to be brought in to deal with the problem, and dealing with it was a long and expensive process.
The news reports that I have seen so far on this have been vague and confused. I was hoping that something more solid would turn up later, but so far nothing has.
I was wondering if anyone had any substantial information on:
a) What took place, particularly with regards to how it started,
b) What was affected,
c) How long it took to get under control, and
d) what temporary and permanent measures were taken to deal with it.
It would also be interesting to hear what measures anyone else has taken to prevent a similar or more serious problem from occurring in their own SCADA, HMI, or other system. I suspect that the typical SCADA, HMI, or plant historian system would be much more vulnerable than was the case in this instance.