Security Decisions in Modbus Industrial Systems
Learn about Modbus security in industrial automation, including vulnerabilities, fixes, and alternative solutions.
There are many pros and cons associated with the integration of security on existing Modbus systems. The primary driver for security introduction is the addition of TCP/IP networking to utilize cloud networking, and this brings with it many potential vulnerabilities. Concern for industrial control systems security goes well beyond commercial realities, extending to homeland security as nation-state security apparatus consider these control systems as high priority targets.
In this article, we'll discuss when Modbus is the correct choice, alternatives, and why you should care about security for industrial control systems.
Modbus Security Issues
Modbus/Modbus TCP by itself exhibits many security problems due to a lack of a complete seven-layer OSI model that incorporates security in its design. Unauthorized access or communications errors can seriously compromise performance with disastrous results. Backdoors and exploits can allow bad actors to hack systems and cause misuse or failure of control.

These problems with Modbus are well understood, but it is useful to summarize them briefly here:
- Lack of message confidentiality
- No protocol intrinsic robust integrity checks on communications at higher layers
- Lack of standardized authentication
- Potential reliability issues of network communications
What do these security issues lead to?
The Consequences of Unsecured Systems
The lack of a formal session structure can open systems up to the possibility of injected command messages. For example, an attacker can send an illegal command into a system, and the Modbus slave devices may return an illegal function exception message. Detection of this return tells the attacker a control system is present, enabling reconnaissance. Likewise, illegal address exception responses generated for queries that contain an illegal slave address can help an attacker gather more information about the target.
Several potential mechanisms allow for a denial of service (DoS) attack, so Modbus systems have been adopting newer standards that resolve such problems.
The need to focus on cybersecurity would seem obvious but when is the effort misspent and how much is too much?
The nature of the Modbus network infrastructure already in place but decisions are complicated by the degree of investment an owner is prepared to commit to change. A half-baked system is almost as bad as no system at all.
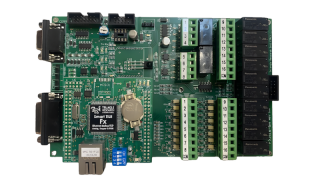
However, if the system is a straight out simple serial interface Modbus RTU (Remote Terminal Unit) or the four-layer TCP-Modbus that incorporates ethernet frame encapsulation, significant improvement is required. If someone is unable or unprepared to make the necessary investment, it makes sense to consider if Modbus is the right choice going forward.
What are our options?
Modbus Security Solutions: Modbus TCP
Modbus/TCP security protocol is an extension of the long-standing Modbus/TCP protocol that utilizes ‘Transport Layer Security’ (TLS) to provide a security level applicable to industrial control systems. It contains many expected conformance levels and compliance requirements. TLS encapsulates the legacy headers of MBTCP for backward compatibility while adding vendor-specific rules-based authorization and certificate-based authentication.
Modbus security is an excellent system for securing industrial control systems by encapsulating packets inside a well-established, standardized protocol. It slides into an existing network structure very easily. With this option comes the possibility of maintaining privacy, incorporating cryptography with digital certificate secure key management and ensuring the reliability of communications link through high-level message integrity checking.
This solution seems to offer everything required for a secure network, along with near-ubiquitous support from web-browsers. However, security attacks are commonplace and on-going. Examples include padding attacks, browser exploits, protocol weakness exploits, and bugs.
OPC UA Security
There are other options than using the Modbus security protocol available, as well.
The OPC Unified Architecture (OPC UA) has tremendous cross-platform support with robust built-in security inside a full communications stack.
Many security vulnerabilities have also been found associated with this protocol. Experts at Kaspersky Lab, however, indicated after a detailed review that they ‘had never seen a configuration that would allow a direct attack from the internet’ and that most vulnerabilities would require access to the local network.
Denial of Service (DoS) attacks appear to be a problem irrespective of solution chosen, but Kaspersky identified this posed a serious threat to industrial process control systems, and the OPC Foundation was quick to release patches for developers to integrate.
A Third Option: OPC UA/Modbus Hybrid
It may be best to use a hybridized system utilizing OPC UA / Modbus converters. If the addition of security is part of an upgrade path that includes ‘smart’ factory or control changes incorporating cloud integration, then migrating an architecture towards ecosystems like Microsoft’s Azure IoT Suite Connected Factory solution could make sense.
IoT gateways with inbuilt Modbus/MQTT (MQ Telemetry Transport) converters are available so you can mix and match to get the best combination solutions. Built-in, the overall system as simple to support.
Why You Should Care About Security in Industrial Control Systems
At the surface level, when all you want is to do is monitor some temperatures and adjust valve settings, added complexity seems ridiculous. However, consider future requirements. Is it conceivable that some manner of remote-control feature now required to manage the system from a remote location? If so, security becomes a serious issue.
If safe operation could depend upon user capability in the future, then authentication is a must.
Don’t just consider the requirements of now—try to allow for the needs of a growing system and mitigate stakeholder investment risk. Regardless of the chosen solution, security requirements and the ramifications of not accounting for this in industrial control are only going to increase over time, and it is essential system architects retain familiarity with this area moving forward.

 Facebook
Facebook Google
Google GitHub
GitHub Linkedin
Linkedin